If you want to protect your online activity, you may have heard of VPNs and proxy servers. But what are they, and how do they work? In this article, you will learn the differences and use cases of proxies and VPNs, as well as their advantages and disadvantages. We will compare their key features like privacy and security – and you will learn how to choose the best tool for your needs and preferences.
What Is a Proxy?
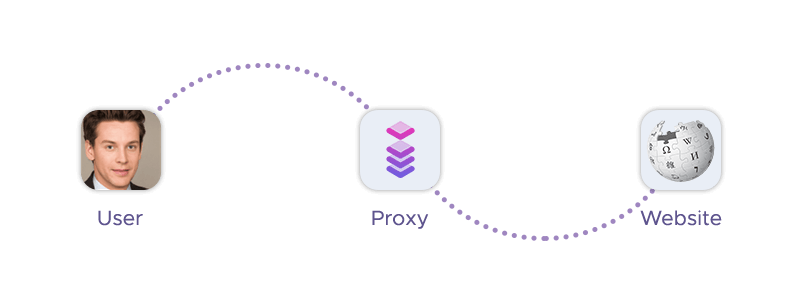
A proxy server is a computer that acts as an intermediary server between your device and the web. It receives and sends data on your behalf, hiding your original IP address and location from the websites you visit.
How proxies work depends on the type of proxy you use. Generally, when you use a proxy, your request is sent to the proxy server instead of the web server. The proxy then forwards your request to the web server and returns the response to you. Sometimes, the proxy may cache the response and deliver it to you directly, without contacting the web server. Many proxy servers can secure your browsing and protect your anonymity.

Types of Proxies
There are different types of proxies – and they vary in their level of functionality, security, and privacy:

- Forward proxy routes your outgoing requests to the web server, hiding the user's IP address and location. You can use a forward proxy to browse the internet anonymously, access geo-restricted content, or scrape the web.
- Transparent proxy does not modify your requests or responses, except for adding an
X-Forwarded-Forheader that reveals your IP address. Transparent proxies are often used by ISPs, schools, or organizations to filter or monitor web traffic. - Anonymous proxy modifies your requests to hide your IP address, but still reveals that you are using a proxy. Anonymous proxies can provide some level of privacy and security, but they may not be able to bypass some strict firewalls or anti-proxy systems.
- Distorting proxy modifies your requests to hide your IP address, but instead of using its own IP address, it uses a fake or random one. Distorting proxies can provide some level of privacy and security, but they may also raise suspicion or trigger captchas.
- Datacenter proxy is a proxy that is hosted on a server in a datacenter, rather than on a residential or mobile device. Datacenter proxies are fast, cheap, and reliable, but they may also be easily detected and blocked by some websites.
- Residential proxy is hosted on a residential device, such as a computer or a smartphone, using a real IP address assigned by an internet service provider. Residential proxies are more natural and trustworthy, but they may also be slower, more expensive, and less stable.
- Public proxy is freely available for anyone to use, without requiring authentication or payment. Public proxies are easy to find and use, but they are also risky, unreliable, and overused.
- Shared proxy is used by multiple users at the same time, sharing the same IP address and bandwidth. Shared proxies are cheaper and more accessible, but they may also be slower, less secure, and more prone to blocks.
- SSL proxy supports the Secure Sockets Layer (SSL) protocol, which encrypts the data between your device and the proxy server. SSL proxies can provide more security and privacy, but they may also require more configuration and resources.
Proxy Advantages
If you use a proxy server correctly, it can offer you these key benefits:
- Anonymity: Proxy servers can hide your IP address and location from the websites you visit, making you more anonymous and protecting your privacy.
- Security: They can encrypt your traffic, filter out malicious content, and prevent hackers from accessing your encrypted data.
- Performance: They can compress and cache your traffic, reducing your bandwidth usage and improving your loading speed.
- Access: They can bypass geo-restrictions and censorship, allowing you to access blocked or restricted content and services.
- Control: They can also monitor and regulate your network activity, enabling you to enforce policies, block unwanted websites, and manage your bandwidth.
What Is a VPN?
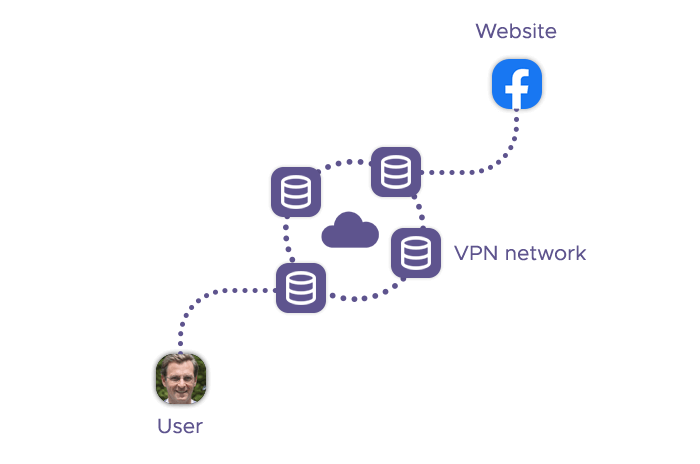
VPN stands for Virtual Private Network, and it is a software-based tool that provides an end-to-end encryption between your device and a VPN server. How VPN works is that it encrypts your sensitive data before it leaves your device, and sends it to one of the VPN providers’ servers around the world. This way, your online privacy is improved – and your data is protected from anyone who might intercept it, such as hackers, ISPs, or governments.
Virtual private networks use different encryption protocols, such as OpenVPN or WireGuard, to secure your data and ensure its integrity and confidentiality. VPNs can enhance your online privacy by hiding your IP address and location, preventing your online activity from being monitored or logged, and allowing you to access geo-restricted or censored content.
VPN Advantages
Using a VPN service nets you these benefits. If you compare proxy vs VPN, you’ll notice they’re pretty similar:
- Privacy: A VPN service can hide your IP address and location from the websites you visit, making you more anonymous and protecting your privacy.
- Security: VPNs can encrypt your traffic, filter out malicious content, and prevent hackers from accessing user data
- Performance: They can compress and cache your traffic, reducing your bandwidth usage and improving your loading speed.
- Access: They can bypass geo-restrictions and censorship, allowing you to access blocked or restricted content and services.
- Versatility: They can also work with any device and any web app that uses the internet, such as browsers, streaming services, games, and torrents.
When to Use a Proxy?
The proxy vs VPN debate comes down to your use case – proxies are good for:
- Web scraping: Proxy servers can help you collect data from web pages by hiding and rotating your IP address, avoiding anti-bot measures.
- Geo-spoofing: They can help you access geo-restricted or blocked content and services by changing your IP address and location.
- Online performance: They can help you improve your online speed and bandwidth by compressing and caching your traffic.
- Network control: They can also help you monitor and regulate your network activity, such as blocking unwanted websites or managing your bandwidth.
When to Use a VPN?
On the other hand, a VPN service is good for:
- Online security: VPNs can help you secure your online activity and protect your data from hackers, ISPs, and governments by encrypting your traffic and hiding your IP address and location.
- Online privacy: They can help you enhance your online privacy by preventing your online activity from being tracked or logged by your ISP, government, or other third parties.
- Online access: A VPN server can help you bypass geo-restrictions and censorship, allowing you to access blocked or restricted content and services.
- Online versatility: They can work with any device and any application that uses the internet, such as browsers, streaming services, internal networks, online games, and torrents.
Proxy vs VPN: Comparison Table
Let’s analyze the key differences of these two technologies:
| Criteria | Proxy | VPN |
|---|---|---|
| Security | Proxies typically do not encrypt data, except for SSL or HTTPS proxies. They may reveal your IP address or that you are using a proxy. | A VPN server encrypts your traffic and hides your IP address and location. They prevent your online activity from being intercepted or logged. |
| Privacy | Proxy servers can hide your browsing activity from your ISP, but they may not protect you from third-party trackers, such as cookies or ads. | VPNs can hide your browsing activity from your ISP and third-party trackers, as well as bypass geo-restrictions and censorship. |
| Cookies | Proxy servers can block or delete cookies, but they may not be effective against other types of trackers, such as fingerprinting or web beacons. | VPN connections can block or delete cookies, as well as other types of trackers, by using additional features, such as ad blockers or anti-malware. |
| Cost | Proxy servers are more expensive as they’re typically used in commercial activities. | VPNs are generally cheaper. security. Some VPNs offer free plans, but they may have restrictions on data, speed, or servers. |
| Internet connection speed | A proxy server is faster than VPNs, as most proxies don’t encrypt traffic. However, they may also be slower due to server congestion or poor quality. | VPNs are slower than proxies, as they encrypt your traffic. However, they may also be faster due to compression, caching, or better server quality. |
| Setup and configuration | Proxies are easy to set up and use, as they only require entering the proxy server address and port in your browser or app settings. | VPNs are more complex to set up and use, as they require installing a VPN client and choosing a VPN protocol and server. |
| Compatibility | Proxies are compatible with any device and app that supports proxy server settings, but they only work with one app or browser at a time. | VPNs are compatible with any device and app that uses the internet, but they may require additional configuration or software for some devices or apps. |
Can I Use VPN and Proxy Together?
It is not a good idea to use VPN and proxy together, as it can cause more problems than benefits. Here are some of the reasons why you should avoid using both services at the same time:
- Reduced speed: Using a proxy and a VPN together will slow down your internet connection significantly, as your data will have to pass through multiple servers and encryption layers. This can affect your browsing, streaming, gaming, and downloading experience.
- Increased complexity: You’ll have to deal with more configuration, troubleshooting, and potential compatibility and connectivity issues. You may also face more errors, blocks, or captchas from certain websites.
- Diminished security: Using VPN and proxy server together will not increase your security or privacy, as the proxy will not encrypt your traffic or hide the fact that you are using a VPN. In fact, the proxy may expose your IP address or leak your data to third parties, especially if it is a free or public service.
Should I Use a Free Proxy or a Free VPN?
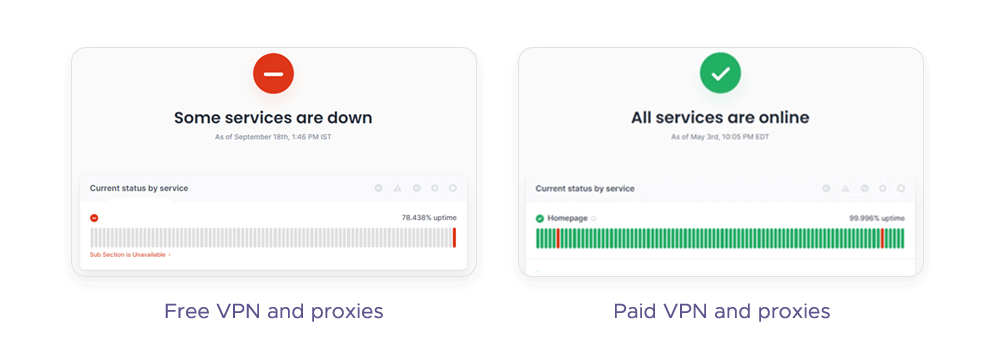
When choosing between VPN or proxy server, it’s tempting to try a free option – but that might be a bad idea. The dangers of free proxy vs free VPN are as follows:
Privacy risks: A free VPN may not encrypt your traffic, leaving your data exposed to hackers, ISPs, or governments. Some free services may use weak or outdated encryption protocols that can be easily cracked.
Risk of traffic monitoring: Free VPNs may monitor your online activity and collect your personal information, such as your IP address, browsing history, or device details. They may then sell your data to third parties, such as advertisers, marketers, or malicious actors.
Malware-ridden ads: Free proxy servers may inject ads into your browser or device, which can be annoying and intrusive. Some of these ads may contain malware, spyware, or viruses that can harm your device or steal your data.
Poor connectivity: Free proxy connections may offer slow and unstable connections, as they have limited bandwidth and server capacity. They may also be easily detected and blocked by some websites, especially video streaming services, which can limit your access to content.
Cookie theft: A free proxy server may steal your cookies, which are small files that store your preferences and login details on websites. It may then use your cookies to impersonate you, access your accounts, or perform fraudulent transactions.
What Should You Use, a VPN or Proxy Server?
Your choice between a proxy server and a VPN depends on your needs and preferences. Both tools can change IP addresses and locations, but they have different strengths and weaknesses:
Coverage: How many geolocations can the given VPN or proxy server offer? Typically, a proxy server works better in this regard: For instance, Infatica offers over 150 geolocations for its residential proxies. VPN servers, on the other hand, are usually less plentiful.
Encryption: Is your private data safe? A typical proxy server does not encrypt your internet traffic, except for SSL or HTTPS proxies, while VPNs encrypt your traffic by default.
Logging: How much of your online activity is recorded or stored by the proxy or VPN provider? Both VPNs and proxy servers may log your IP address, browsing history, or device details. Many VPNs claim to have a no-logs policy or a minimal-logs policy, but this is often not the case.
Speeds: How fast is your internet connection when using proxy vs VPN? Proxies are faster than VPNs, as they do not encrypt your traffic, but they may also be slower due to server congestion or poor quality. However, the performance of both network utilities can be improved via compression, caching, or better server quality.
Payment: How much do you have to pay to use the service? Proxies are generally more expensive as they offer more commercial use cases, while VPN services can be cheaper thanks to frequent sales and special offers. As for free proxies or VPNs, they may have limited functionality, reliability, and data security.
Hiding IP: How well can the service conceal your real IP address and location from the websites you visit? Unfortunately, in this proxy vs VPN issue, both technologies can be error-prone and be detected.
Safe: How trustworthy and reputable are your proxy or VPN provider? If you want to avoid malware, spyware, or viruses, use ethical proxy service providers like Infatica: These companies source their IP addresses from consenting users.
Final Words
Proxies and VPNs are both tools that can change your IP address and location, but they have different levels of coverage, encryption, logging, speeds, payment, and safety. Proxies are cheaper and faster, but they have less coverage and encryption. A VPN connection is more versatile and reliable, but it may also be more expensive and slower. The choice depends on your needs and preferences. We hope this article helped you understand the difference between a proxy and VPN and their use cases.